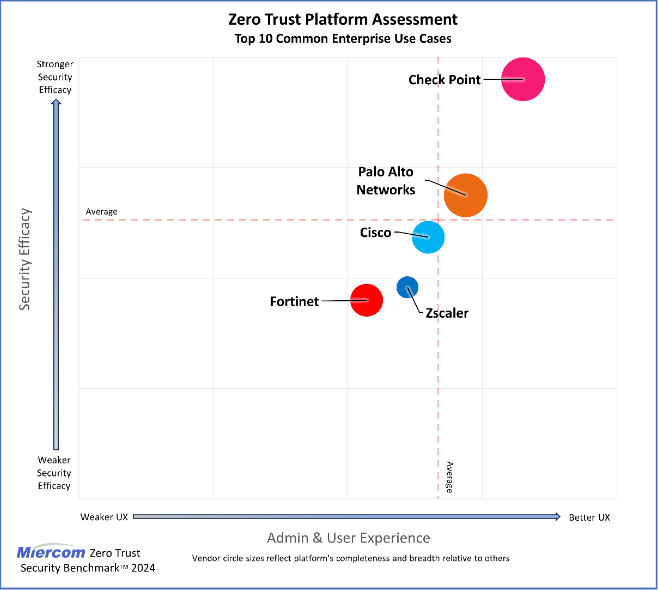
In the dynamically changing field of cybersecurity, adopting a Zero Trust architecture is essential for organizations looking to strengthen their security posture. This approach emphasizes centralized management, deployment flexibility, and continuous verification of users and devices, thereby eliminating risks associated with misconfigurations and human errors. The Check Point Infinity platform has demonstrated the highest level of security and the best administrative and user experience among the evaluated Zero Trust solutions.
Three fundamental pillars of the Zero Trust strategy:
-
Centralized management and usability of multiple security components – A Zero Trust platform should enable centralized management that integrates and controls various security elements from a single interface. This functionality simplifies the management of complex security policies across different environments, minimizes the risk of errors, and provides administrators with tools to effectively manage the security of networks, cloud, SaaS applications, endpoints, and email protection.
-
Hybrid architecture and deployment flexibility – The ability to support a hybrid architecture with various deployment models is essential. The platform must be compatible with on-premise firewalls, virtual firewalls, cloud firewalls, and Firewall-as-a-Service (FWaaS) services, ensuring consistent policy enforcement regardless of asset location.
-
Ability to implement Zero Trust principles – The core of Zero Trust is continuous verification of users, devices, and applications, including modern technologies such as cloud services and IoT devices. The platform must enforce access controls based on the principle of least privilege, ensuring that entities have access only to the resources necessary for their tasks.
Benefits for administrators and users
The quality of the user interface and administrative environment is crucial for the effective management of security settings. An intuitive interface allows for:
- Quick and efficient updates of settings.
- Informed decision-making about network activities.
- The ability to request remediation of unauthorized restrictions, reducing frustration and increasing security.
Evaluation of the Check Point Infinity platform
According to an independent evaluation by Miercom, which included an analysis of 10 common Zero Trust implementation tasks, the Check Point Infinity platform outperformed competing products in several key areas:
- Security effectiveness: Check Point excels in threat prevention and response, providing comprehensive protection.
- User experience: An intuitive interface and streamlined management processes significantly enhance the administrative and user experience.
- Zero Trust implementation: The platform excels in securing modern IT environments against persistent and evolving threats.
Zero Trust architecture represents a fundamental step for organizations aiming to effectively protect their digital assets and minimize risks. Adopting robust solutions like Check Point Infinity allows businesses to implement comprehensive security strategies with maximum efficiency and ease of management.
Read Miercom’s NGFW Security Benchmark Report to learn more about the security effectiveness of the industry’s most popular firewall vendors.


