In today’s environment—where organizations require sovereign data protection, high‑level compliance, and modern device management—Microsoft Intune alone is often no longer enough. The combination of BlackBerry® UEM and Microsoft® Intune offers the ideal solution, merging Microsoft 365 productivity with secure container technology, certified encryption, and a level of data control that OS‑centric solutions simply cannot provide.
Together, these technologies form a modern, security‑driven mobility ecosystem that is fully prepared for the upcoming era of post‑quantum threats.
Expanded Security Layer: Intune + BlackBerry UEM
BlackBerry UEM extends Microsoft Intune in several critical security areas. The following comparison highlights the differences between native Intune capabilities and what BlackBerry adds:
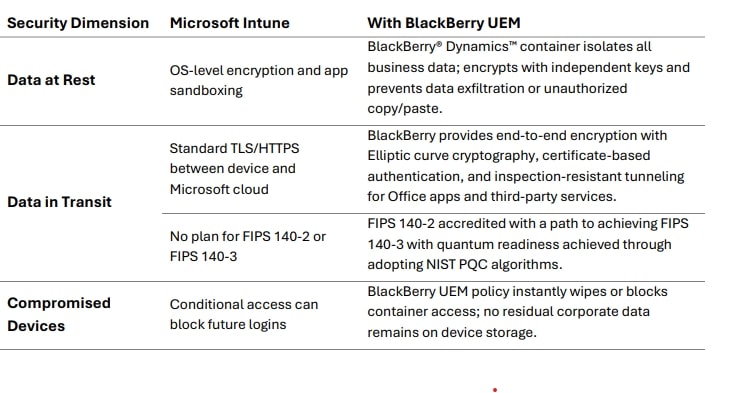
This layered architecture ensures zero data leakage—even if the OS or an application is compromised. It delivers:
- separation of work and personal data,
- true, risk‑free BYOD,
- data‑in‑transit protection aligned with future FIPS 140‑3 requirements,
- quantum‑ready architecture.
Real-Time Conditional Access and Instant Policy Enforcemen
The integration of BlackBerry UEM with Microsoft Entra ID enhances Conditional Access with additional security variables, such as:
- device health and container integrity,
- certificate validity checks,
- real‑time granular access control,
- per‑app VPN routing through BlackBerry® Access for secure cloud connectivity.
The result is an architecture where only trusted, compliant, and encrypted devices can access sensitive data—significantly reducing the risk of compromise.
Secure Productivity in Microsoft Office Applications
Organizations using Microsoft 365 can leverage full-featured mobile Microsoft Office apps—securely and without compromise—thanks to BlackBerry® Bridge. It enables:
- opening, editing, and saving Office documents inside the Dynamics container,
- secure collaboration via Outlook and Teams,
- unified enforcement of DLP, encryption, and Conditional Access across both platforms.
This ensures unrestricted, secure productivity, ideal for large teams and regulated industries.
Extensive Enterprise App Ecosyst
The BlackBerry Dynamics SDK enables internal and partner apps to run inside a secure environment and provides:
- encrypted storage for every Dynamics app,
- controlled data sharing between applications,
- certificate‑based access validation,
- simple “wrapping” of existing apps without modifying code.
The BlackBerry ecosystem today includes 127+ enterprise-grade applications from more than 100 ISV partners. Intune users gain access to a broader and more secure app portfolio than with any other UEM solution.
Enhanced User Experience – BlackBerry Work
BlackBerry® Work is designed for environments with strict security requirements and offers:
- FIPS‑validated encryption,
- OS‑independent container architecture,
- unified UI for email, calendar, and contacts,
- guaranteed separation of personal and corporate data.
Unlike Outlook Mobile—which is built on a consumer-oriented foundation—BlackBerry Work ensures that corporate data never leaves the secure container.
Microsoft 365 integration remains fully preserved, while the organization gains maximum possible security.
BlackBerry UEM + Microsoft Intune: The Best Combined Solution
In the hybrid work era, device management alone—or app control alone—is no longer sufficient.
The combined strength of BlackBerry UEM and Microsoft Intune delivers:
- sovereign data protection,
- certified encryption,
- reduced TCO,
- secure access to Microsoft 365,
- architecture ready for post‑quantum threats,
- consistency across BYOD and corporate devices.
Together, these solutions represent the highest standard of modern, secure, and scalable mobility. Organizations gain reliable data protection, unified management, and uncompromised productivity—while staying prepared for upcoming security challenges, including post‑quantum risks.
For more information, please download: